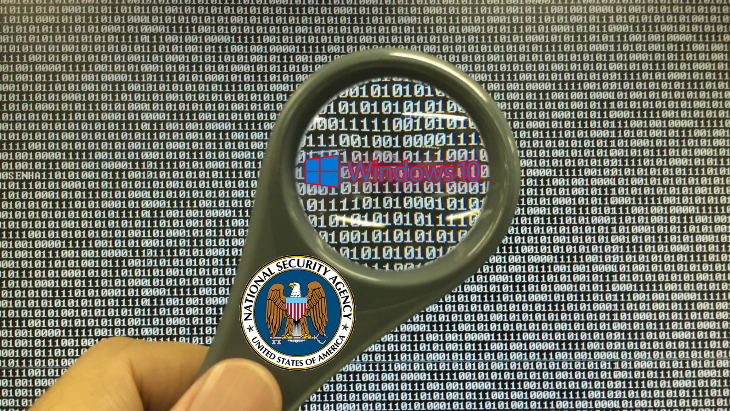
The National Security Agency (NSA) of the United States has warned all Windows 10 users to update their OS, after a critical vulnerability was discovered.
A mere day after Windows 7 was discontinued, The NSA has issued a statement, warning all 900 million users to update their copy of Windows 10 due to a “critical vulnerability.”
The official statement reads as follows:
NSA has discovered a critical vulnerability (CVE-2020-0601) affecting Microsoft Windows cryptographic functionality. The certificate validation vulnerability allows an attacker to undermine how Windows verifies cryptographic trust and can enable remote code execution. The vulnerability affects Windows 10 and Windows Server 2016/2019 as well as applications that rely on Windows for trust functionality. Exploitation of the vulnerability allows attackers to defeat trusted network connections and deliver executable code while appearing as legitimately trusted entities. Examples where validation of trust may be impacted include:
- HTTPS connections
- Signed files and emails
- Signed executable code launched as user-mode processes
The vulnerability places Windows endpoints at risk to a broad range of exploitation vectors. NSA assesses the vulnerability to be severe and that sophisticated cyber actors will understand the underlying flaw very quickly and, if exploited, would render the previously mentioned platforms as fundamentally vulnerable. The consequences of not patching the vulnerability are severe and widespread. Remote exploitation tools will likely be made quickly and widely available. Rapid adoption of the patch is the only known mitigation at this time and should be the primary focus for all network owners.
In layman’s terms, hackers have discovered a vulnerability in Windows 10 that could (for example) issue a fake update that grants them total control and oversite over a user’s computer.
The NSA advises “installing all January 2020 Patch Tuesday patches as soon as possible to effectively mitigate the vulnerability on all Windows 10 and Windows Server 2016/2019 systems.”
With the NSA acting before Microsoft, some have shown more concerns about why exactly they would speak out. While the US Department of Defense confirmed they would be running Windows 10 back in 2018, it seems logical (and we hope) they would utilize more sophisticated technology, minds, and anti-hacking measures to be unaffected by matters such as this.
Their concerns may have arisen thanks to Windows 10’s “Update Delivery Optimization.” It allows updates to happen from other PCs on your local network. If hackers could exploit Windows 10 into thinking malicious code is part of a normal Windows 10 update, it stands to reason the virus could spread through a system.
The news was seemingly first broken by Will Dormann, a Vulnerability Analyst at the CERT Coordination Center. He tweeted on January 13th “I get the impression that people should perhaps pay very close attention to installing tomorrow’s Microsoft Patch Tuesday updates in a timely manner. Even more so than others. I don’t know… just call it a hunch?”
Cyber crime journalist Brian Krebs reported (via Krebs On Security) later that day, that they had heard rumors from their sources claiming “Microsoft has quietly shipped a patch for the bug to branches of the U.S. military and to other high-value customers/targets that manage key Internet infrastructure, and that those organizations have been asked to sign agreements preventing them from disclosing details of the flaw prior to Jan. 14, the first Patch Tuesday of 2020.”
His report mentions the vulnerability came via crypt32.dll (a Windows module that Microsoft claims it handles, quote: “certificate and cryptographic messaging functions in the CryptoAPI”). While it is not mentioned in the NSA’s announcement, Krebs did state crypt32.dll could be used to “spoof the digital signature tied to a specific piece of software.”
On January 14th, Krebs updated his article, stating the NSA’s Director of Cybersecurity Anne Neuberger hosted a media call that morning to report the vulnerability discovered by “NSA researchers” to Microsoft. He also stated that “this was the first time Microsoft will have credited NSA for reporting a security flaw.”
When asked why the NSA focused on that flaw, Neuberger reportedly stated there was concern that it “makes trust vulnerable.” The NSA declined to give further details to Krebs, such as when they discovered the flaw.
Krebs would later state on Twitter that while this was not the first time the NSA had taken public credit for discovering a flaw, it would be a new approach in the future.
“Sources say this disclosure from NSA is planned to be the first of many as part of a new initiative at NSA dubbed “Turn a New Leaf,” aimed at making more of the agency’s vulnerability research available to major software vendors and ultimately to the public.
The NSA’s Neuberger said this wasn’t the first vulnerability the agency has reported to Microsoft, but it was the first one for which they accepted credit/attribution when MS asked.”
Windows 10 has been begrudgingly accepted by most due to it being a free upgrade to Windows 7 and 8 for a time. Others expressed great concern over Windows 10’s privacy due to features such as Cortana– a digital “personal assistant” that responds to voice and your activities to help preempt questions and pre-load web-pages.
Others still claim that Windows has worked secretly with the NSA to install digital back-doors into their OS, to allow them to spy on users without a warrant. Suffice to say, no formal evidence or charges have arisen. A far more pressing concern many users had were its forced updates and reboots, along with the changes to their start menu to highly resemble a smartphone screen (including adverts for games).